?If you Think you Know-It-All about Cyber Security, this Discipline was probably Ill Explained to You?– Stephane Nappo
Gone are the days when we had to wait endlessly for communicating something to our loved ones.
Phones came as a savior which helped us to connect with others at the click of a button. In due course of time, these little devices became more and more sophisticated and have now become an inseparable aspect of our lives.
But, do you know that this little companion of yours, can in fact become a medium for a cyber attack too? Yes, you heard it right; phone calls can tantamount to an entirely different category of cyber attack and this forms the crux of the answer to the question of What is Vishing.
In this blog, we shall try to understand What is Vishing in Cyber Security. We will look at what is vishing attack in terms of its types and examples. Moreover, the query of what is a vishing attack, shall be sought to be understood in its entirety through differentiating vishing from phishing attacks and smishing.
If you are curious about knowing more about another very common form of Cyber Attack, known as Clickjacking, do read our blog on ?What is Clickjacking?: All that You Need to Know?
What is Vishing?
Vishing is a type of cyber crime which operates as a phone scam wherein callers (cyber criminals) persuade/force/convince you to reveal sensitive, confidential and personal information over the call.
Vishing Attacks are considered to be a combination of Voice and a Phishing Attack. In other words, Vishing can be understood as a voice based phishing attack, meant to extract personal or financial information from the victims over a fraudulent phone call.
The basis of vishing lies in convincing the victims that they are doing the right thing in revealing their information to the caller. This is ensured through various means which we shall look at in the next section.
Sometimes, the cybercriminals even resort to forceful and strong language in intimidating the victims for revealing data. Moreover, technological advancements have made it even easier to contact more and more people.
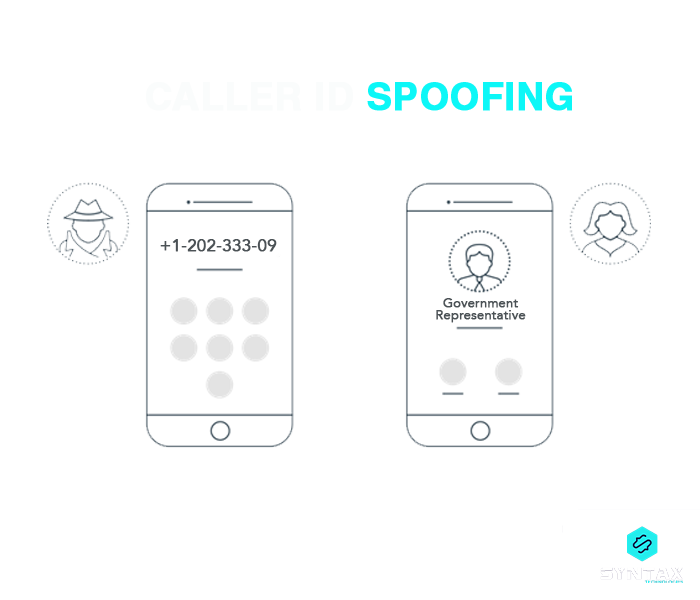
Hundreds of calls can be placed at a time using VoIP (Voice over Internal Protocol) Technology and the Caller ID can be spoofed in order to dupe the victims into believing that the call is from a trusted source.
In trying to understand, what is a Vishing Attack; you should remember that it a kind of cyber attack wherein scammers make use of social engineering techniques for making victims reveal their confidential information.
Social engineering operates as a manipulation technique which is based on the fundamental human instinct of trust for stealing corporate and personal data. A vishing attack is essentially unpredictable and is executed with detailed planning, causing immense harm to the victims.
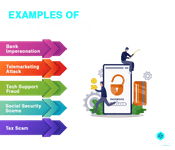
What is Vishing Attack: Examples
In this section of the blog, we shall look at What is Vishing in terms of some of the common instances which are reflective of a Vishing Attack.
- Bank Impersonation
Under this type of Vishing Attack, a cyber criminal might impersonate the Bank, Credit Card Company or other financial institutions which the victim has reasons to trust. Through the spoofed phone call, the victim is usually told by the scammer that either there has been some suspicious activity at the end of his band account or there is some issue with his credit card and so on.
Consequently, the victims are asked to confirm their bank details, mailing addresses, account numbers and so on.
- Telemarketing Attack
The chance to grab a free prize is a lucrative prospect for each one of us. Unfortunately, cyber criminals seek to exploit this basic human instinct as bait for alluring victims. Vishing takes place when victims are instigated to divulge confidential information in lieu of claiming the free prize.
- Tech Support Fraud
This is an instance of a Vishing Attack wherein Callers adopt the spam identity of a tech support from a reputable company. Victims are falsely informed of unusual activity at the end of their account and asked to confirm their account details.
At times, they are also asked to provide their email address, to which they are promised of being sent a software update, which often ends up being a way to implant malware in the victim?s system.
- Social Security Scams
Cyber criminals might pose as medical representatives or government agents in order to elicit bank account details or Medicare number from the victim. Through this, the crook might use the healthcare benefits of the victim.
Additionally, there might be instances wherein victims are told that their social security number has been suspended and they are asked to confirm the same. This relates closely to potential vishing scams and identity theft, often perpetrated under the guise of the Social Security Administration or other authoritative bodies.
- Tax Scam
The victim is told of some kind of anomaly at the end of his tax returns through a pre-recorded voice message. He is intimated to call back or else threatened of a warrant for arrest being issued in his name. The scammer usually makes use of a spoofed caller ID in order to allegedly pretend that the call is from the IRS (Internal Revenue Service).
?
Types of Vishing Attack
Knowledge of what is Vishing Attack cannot be complete without considering the different types and forms of the same.
- VoIP
This technology facilitates the creation of fake numbers which can easily be used to hide real identity. These numbers are not easily traceable and can be made to appear local.
Moreover, cyber criminals also use the VoIP technology to create numbers which appear to come from the police department, government department and so on.
- Dumpster Diving
As the name suggests, this technique involves diving into dumpsters behind office buildings, banks and other random organizations, with the objective of collecting valid phone numbers.
Cyber criminals often end up acquiring sufficient information which could facilitate a Vishing Attack against an individual.
- Wardialing
This is perhaps one of the most common forms of Vishing. It involves numerous automated calls being made to hundreds or thousands of numbers. More often than not, the cyber criminal uses specific software to call area codes, with a pre-recorded message which involves the name of a local organization, local bank, police department and so on. The victims are often threatened with voice messages which command them to call back the scammers. Besides, they are also urged to divulge their financial details, social security information and much more. The victim is made to believe that the information is necessary in order to ensure that the victim?s account has not been compromised.
- Caller ID Spoofing
This strategy is used by cyber crooks to take cover behind the garb of fake numbers and caller Ids. Their name is listed as unknown or they put up the pretense of being a legitimate caller from some legitimate governmental department.
Difference between Vishing, Phishing and Smishing
The domain of Cyber Security is an expansive one. Moreover, it has come to harbor diverse kinds of digital attacks and threats. Many of these attacks have overlapping features and are often assumed to be similar to each other. However, if you really wish to understand the nitty-gritty of the field, it is not just enough to know what is vishing, but also make sense of the difference between vishing and two very closed related terms to it, phishing and smishing.
How to Detect a Vishing Attack?
It is often said that the best way to avoid a vishing attack is to ignore one. However, this is easier said than done. Telecoms do have fraud detection systems in place which help in giving some kind of a warning such as ?Scam?, ?Fraud Risk? and so on, on caller id when a suspected malicious call is received. However, this system is not fullproof and cannot be depended upon, to filter all such threatening calls. Hence, it is important to be aware of some of the tell-tale signs of a Vishing Attack.
- The caller claims to represent some federal/governmental agency
It is important to remember that authentic governmental agencies would never seek to initiate contact with you through voice calls, text messages or email and ask you for any sort of financial or personal information. If you do receive a call from someone who claims to be such a legitimate representative, you should at once be skeptical.
- The caller asks you to provide sensitive or confidential information
Follow one simple motto, ?never ever real any kind of identifying information? to anyone. This holds true in all situations and even when the scammer seeks to convince you by validating some of your existing information, you should not fall prey to such crooks.
- Usually, there is a sense of urgency
In a vishing attack, a cyber criminal generally seeks to play upon your instincts of fear and greed. At times, scammers intimidate their victims with threats of arrest, account suspension, social security benefits suspension and so on. In such situations, it is important to remain calm and refrain from giving into such claims.
What is Vishing: Prevention Strategies
It is not simply enough to know what is Vishing Attack; on the contrary, it is equally important to be aware of certain precautionary measures which one should take in order to be safe.
- Register to the National Do Not Call Registry
You can add your phone number to this registry free of cost which conveys a message to the telemarketers that you do not want their calls. However, this system is not a full proof barrier against all types of calls, such as those coming from political and charitable groups.
- Do not Share any Personal/Identifying Information over the Phone
You should never share any personal or confidential information over the phone. Authentic organizations never ask or try to convince you to provide them with any of those sensitive information.
- Try to Avoid Calls from Unknown Numbers
Do not be tempted to answer each and every call, especially those which come from unknown numbers. You can let those calls go to voicemail and decide later whether you should call the person back or not. Moreover, you can also avoid vishing by forwarding unknown callers.
- Investigate
Notwithstanding the identity that scammer professes to present, it is always important to countercheck. If the caller tries to allure you with baits of cash money or free prize, always ask them for some sort of a proof by which you can verify what they are saying. Similarly, if someone claims to represent a legitimate organization, ask them for proof of identity. If they refuse to provide any such information, simply hang up.
- Do not Respond to Prompts
Never press buttons, oblige to requests or respond to any prompts, from sources which you fail to understand. The responses are used by cyber criminals to identify potential targets for more robocalls.
- Hang Up
It is important for you to be aware and be alert. The moment you suspect a phone scam through a Vishing Attack, simply hang up.
Recovery and Resilience
You might be aware of what is Vishing; however, there might be a situation wherein you do happen to unfortunately fall prey to a Vishing Attack. In such a situation, what should you do?
- If you happen to suspect a Vishing Scam, report and block the number immediately
- You can also file an official complaint with the Federal Trade Commission
- Whenever you receive calls wherein the caller claims to represent any of the legitimate organization like your bank, governmental agency and so on; try contacting your actual financial authority and inform them about the incident
- If for any reason, you happen to have already shared your financial information, do contact your financial institution immediately and request them to block your credit or debit card immediately, in order to prevent any potential fraudulent transactions
- At the same time, you should update your account credentials in order to make sure that others do not use their current accounts. You can opt for freezing your credit reports
Conclusion
By the end of this blog, I am pretty sure, you must have acquired a fair understanding of what is Vishing. It is definitely a malicious form of cyber attack which has the potential to incur immense damage to the victims concerned. As you seek to understand what is Vishing in Cyber Security; you should see it against the wider backdrop of a Phishing Attack which is a prominent form of cyber attack.
Being aware of different kinds of cyber attacks is crucial in securing a foothold within the domain of Cyber Security. We, at Syntax Technologies, provide you with the exciting opportunity to develop expertise in consonance with the demands of the field. Enrol now for our Cyber Security course.