?There are Cyber Threats out there, this is a Dangerous World, and we have to be Safe, we have to be Secure, no matter the Cost? – Edward Snowden
The increasing reliance on the virtual world has only accelerated the magnitude and frequency of threats posed to the real world.
While there are many different kinds of Cyber Attacks; ARP Spoofing has evolved as a serious form of threat which not only results in leakage of sensitive information, but can facilitate additional forms of attack.
However, before we try to answer the question of what is the aim of an ARP Spoofing attack; it is important to understand the concept of an ARP attack itself.
????If you wish to read more on other such malicious form of Cyber Attacks such as Clickjacking, do read our blog on ?What is Clickjacking??
In order to facilitate communication over a LAN (Local Area Network), it is important to associate the elements of the IP (Internet Protocol) Addresses with the physical permanent address of the machine which is a party to the communication process.
This is where the Address Resolution Protocol (ARP) comes into the picture. ARP can be perceived of as a network protocol which helps in translating IP addresses into a MAC (Media Access Control) address and vice-versa, through sending ARP request packets.
ARP acts as the medium which helps the devices to forge connection with the router and eventually connect to the Internet. However, the issue of an ARP Spoofing Attack arises when these ARP attacks are hijacked or intercepted by hackers.
????In this blog, we shall try to answer the question of what is ARP Spoofing as well as try to look at the different dimensions of an ARP Spoofing Attack. Additionally, we shall also consider some important issues like: ARP Spoofing Prevention Strategies, ways to set up a robust ARP Spoofing Defense mechanism, ARP Spoofing Detection Tactics as well as look at the different ARP Spoofing Tools.
What is ARP Spoofing?
ARP Spoofing Attacks have been facilitated through an unintentional shortcoming of the very mechanism of ARP. The ARP protocol was introduced way back in 1982; however, since security was not such a huge concern, the protocol did not involve any mechanism for validating or authenticating ARP messages.
This implies that any device on the LAN can respond to an ARP request. This lacuna is exploited by Cyber Criminals and form the crux of ARP Spoofing.
ARP Spoofing or ARP Poisoning can be seen as a form of the Man in the Middle Attack (MitM) as it permits the hacker to intercept communication between two devices within a network.
In the first place, the attacker must have access to the specific Local Area Network (LAN). They perform network scanning in order to acquire the IP addresses of minimum two devices within the network.
Next, they make use of a particular ARP Spoofing Tool in order to send out illegitimate ARP requests. These ARP packets are meant to convey the wrong message that the correct MAC address for the two IP addresses is the one belonging to the device of the attacker.
Since, there is no security layer in between; the two devices whose IP addresses had been acquired, end up connecting with the attacker?s device, instead of with each other.
By way of this unintentional connection, the attacker acquires access to all communication between the two devices.
Types of ARP Spoofing Attack
It is important to remember that in order to initiate ARP Spoofing or ARP Poisoning Attacks, a hacker can either wait to receive ARP requests and provide a response or can himself send out unsolicited ARP requests.
The second method has a far greater impact and affects a large number of victims. The act of ARP Spoofing can itself take the form of different types of Cyber Attacks.
- Man in the Middle (MitM) Attack
As the name suggests, ARP Spoofing allows the attacker to position himself in the middle of a communication between any two devices.
By way of responding to the malicious ARP request sent by the attacker; the victim devices end up populating their ARP cache with the MAC address of the attacker, essentially falling victim to an ARP cache poisoning attack.
Consequently, the network traffic is then directed from the targeted device to the attacker?s machine. The ARP Spoofing Tool aids the attacker in stealing or altering information before it is sent to the intended destination.
- Session Hijacking
In this case, instead of modifying information and then forwarding the message to the intended destination; attackers perform a different role.
Hackers steal specific pieces of information such as web cookie, session ID, TCP sequence number and so on, which helps them in falsely assuming the identity of the victim.
This in turn helps them in acquiring access to private systems such as the social media account of the victim.
- Denial of Service (DoS) Attack
As the name suggests, the objective of this type of Cyber Attack is to prevent a device from performing its designated function. This can happen when a machine is overwhelmed by excess traffic. When a hacker sends out an ARP request, they can cause several IP addresses to link to a single MAC address which results in ARP flooding. This results in hampering the performance of all the devices within a particular network.
What is the Aim of an ARP Spoofing Attack?
It is evident that ARP Spoofing is another malicious form of Cyber Attack. The purpose of the same is clearly wicked and evil. In this section, we will look at some of the supposed objectives of an ARP Spoofing Attack.
- ARP Spoofing can facilitate spying on, dropping or modifying traffic. This is caused when false ARP messages adopt the form of a default getaway for a specific subnet. This results in directing all the traffic to the attacker?s device.
- One of the goals of ARP Spoofing is espionage. In order to serve such an objective, the intercepted message is pried upon by the attacker, but is eventually forwarded to the intended destination.
- When an ARP Spoofing Attack takes place in the form of a DoS Attack, it is essentially caused with the goal of disrupting the operation of the entire network which is targeted.
- Since one of the criteria for rendering an ARP Spoofing Attack successful is that the attacker must have access to the Local Area Network; ARP Spoofing increases the threat of Insider Attacks.
What Type of Additional Attack does ARP Spoofing Rely on?
The additional attack that ARP Spoofing relies on is MAC Spoofing. MAC Spoofing is the process of altering the assigned Media Access Control (MAC) address of a networked device. The address is embedded in the Network Interface Controller (NIC) and as such cannot be changed. However, there do exist certain tools and drivers which allow for this MAC address to be changed. This process of changing the address is referred to as MAC Spoofing and is maliciously used to alter the identity of a device. This modification of the address permits the user to sideline access control lists on routers and servers. As a result, a device can impersonate another device on another network or can hide itself within a network.
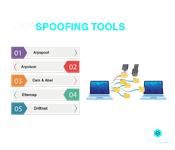
ARP Spoofing Tools
ARP Spoofing is carried out with the help of certain specialised ARP Spoofing Tools. Some of these are:
- Arpspoof
- Arpoison
- Cain & Abel
- Ettercap
- Driftnet
ARP Spoofing Detection Tactics
While an ARP Spoofing Attack can certainly have a lot of negative consequences; there do exist certain ways by which one can detect a case of ARP Spoofing. One of the simplest options is to make use of the Command Prompt Tool on a Windows PC, in order to extract the ARP Cache on the Command Window by entering ?arp -a?. This helps in displaying the existing IP-to-MAC address mappings of the device. On careful scrutiny, if you do find that two different IP addresses happen to be sharing the same MAC address, then it is quite likely that you are a victim of ARP Spoofing.
How to Prevent ARP Spoofing?
In this section of the blog, we shall look at some of the most crucial ARP Spoofing Prevention Strategies which can help in strengthening the ARP Spoofing Defense mechanism.
- Encryption
It is important to remember that this Anti-ARP Spoofing strategy is not meant to prevent the attack in the first place, but it can definitely mitigate its impact. The usage of cryptographic protocols helps in encrypting data prior to their transmission, thereby making it difficult for the hacker to steal sensitive information. Some of these encryption protocols include HTTPS (Hypertext Transfer Protocol Secure), TLS (Transport Layer Security), SSH (Secure Shell) and so on.
- Virtual Private Network (VPN)
This ARP Spoofing Prevention strategy works on the same principle as the previous one, the only difference being that instead of encrypting messages, it provides for an entire encrypted channel of communication. Thus, by using a VPN, devices can connect and communicate with each other through an encrypted and secure tunnel which renders an ARP Spoofing Attack unsuccessful.
- Packet Filters
This ARP Spoofing Defense strategy involves the installation of packet filters which help in scrutinizing all the data packets which are transmitted through a particular network. These packets help in detecting and blocking any packet which is suspected to be malicious as they seem to originate from a distrustful IP address. These packet filters also help in blocking packets which are suspected to have originated from an external source, but is being transmitted internally over a Local Area Network (LAN).
- Static ARP Entries
This Anti-ARP Spoofing mechanism is one of the most effective strategies for ARP Spoofing Prevention. It involves manual mapping of all the MAC addresses within a Local Area Network to their designated IP addresses. By way of adding these individual ARP entries, devices can be made to ignore ARP requests other than those to which it is mandated to respond. This helps in preventing ARP Spoofing attempts. However, such manual updates to the ARP tables become administratively very difficult especially for large organizations.
- Physical Security
Since physical proximity is one of the criteria for mounting an ARP Spoofing Attack, it is important to regulate physical access to the devices within a local network. In case of wireless networks, an attacker would not necessarily require physical access, but even a signal which extends to the nearby area can be sufficient to be exploited. Thus, whether it is the case of wired or wireless network, it is important to make use of technologies which will be able to ensure that only specific managed or trusted devices are connecting to the network.
Conclusion
An ARP Spoofing Attack is quite a persistent threat as it impacts the very core of the network infrastructure. ARP Spoofing dates back to times earlier than most other advanced form of Cyber Threats and Attacks like Clickjacking, Ransomware, Steganography and so on; however, given the nature of the attack, it can only be best addressed through a robust information security program. It is important to incorporate mechanisms which will be able to detect these attacks as well as respond to them in an appropriate manner.
If you wish to know more about the Steganography Attack, read our blog on ?What is Steganography? Everything You Need to Know About It?
Given the soaring magnitude and frequency of Cyber Attacks, a career in the field of Cyber Security has emerged as one of the most lucrative professional avenues. We, at Syntax Technologies, provide you with the exciting opportunity to develop expertise as a Cyber Security Professional. Read more about our Cyber Security Course.